Investigating Universal Analytics

Two common questions when investigating web browsing are: (1) how long did a user spend on a website, and (2) what actions did they take while on it?
We have a number of methods of approximating what the user did and how much time they spent on a page, but browser histories just weren’t designed to comprehensively record all that information. Chrome visit records have a nifty attribute called visit_duration, but it records the total time the page was open, regardless of whether the user was actively looking at it. I have several tabs that are always open in Chrome, and their visit_duration values are over a week.
However, DFIR folks aren't the only ones interested in what people do on webpages. There's an entire multi-billion dollar industry built around it: online advertising. Google is one of the biggest players in online advertising, and thus is also a leader in user-tracking. Being able to track users, build profiles of their behaviors, and see what actions they take on websites is valuable to Google, because Google can then use that information to sell targeted ads at higher prices.
Move Over Google Analytics - Here Come Universal Analytics
None of this is breaking news and the forensics community has known about the value of exploiting Google Analytics (GA) cookies for years. However, like all technology, GA cookies will eventually be replaced with a new and improved version. In fact, Google Analytics' replacement is already here: Universal Analytics. Google now calls the trusty GA system a "legacy" and "outdated":
Universal Analytics (UA) has been out for a while now and is used by plenty of websites "in the wild". However, I have yet to see anything on it from a forensics perspective, probably for a simple reason: they don't look as interesting as the still-prevalent GA cookies. GA sets a variety of cookies, all prefixed with __utm, and they contain quite a few interesting tidbits when decoded. I won't rehash all the GA info, but check out Jon Nelson's write-up if you want a refresher.
Universal Analytics Cookie Structure
The UA cookies are a bit less exciting on the surface. Like GA cookies, they are first-party cookies, which means the website the user is on sets them, rather than a third-party (like Google). The cookies' names are _ga and _gat (both have only a single underscore, not two like GA cookies). The _gat cookie is for throttling, and either isn't set or has a value of 1.
The _ga cookie value looks something like this:
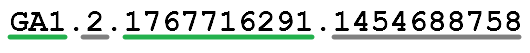
The _ga cookie is made up of four parts:
- GA1 - the version number; GA1 is the only value I've observed
- 2 - the number of . in the domain the cookie is set for (.obsidianforensics.com)
- 1767716291 - randomly generated ID, unique per device
- 1454688758 - epoch timestamp of the first time this user visited the UA property
Parts 1 and 2 aren't very interesting, but 3 and 4 are. The combination of the random ID and timestamp is what Google calls a Client ID. This is what Google uses to track a user across sessions. The _ga cookie is set to expire after two years, which means that as long as the user doesn't clear their cookies it will stick around for quite a while.
The relative scarcity of interesting data embedded in the UA cookie compared the GA cookies may be disappointing. The UA cookie gives us the time of a single previous visit, while the GA __utma cookie alone had three embedded timestamps, and the other __utm cookies had even more interesting information. However, in certain situations, the UA cookie can unlock a large amount of interesting information.
User Explorer Reports
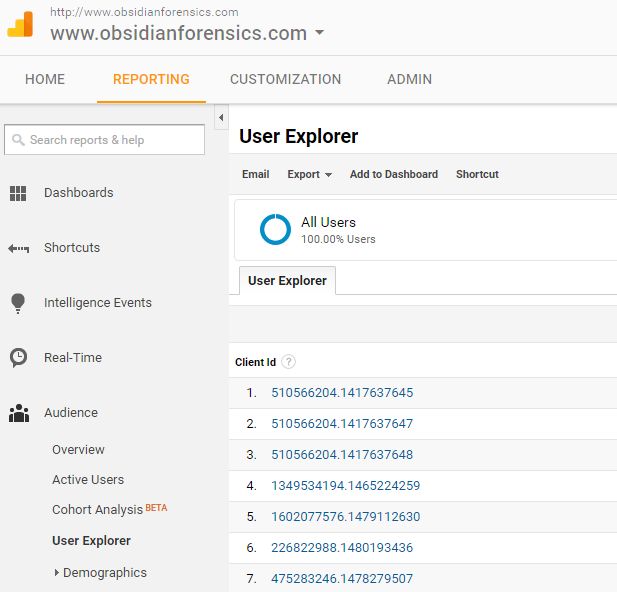
Google Analytics has a reporting interface that countless webmasters use to see how visitors are using their site. It has myriad options and I'm a novice at using it. I have UA installed on this website and I occasionally poke around through the analytics reports. Recently, I found a new section: User Explorer.
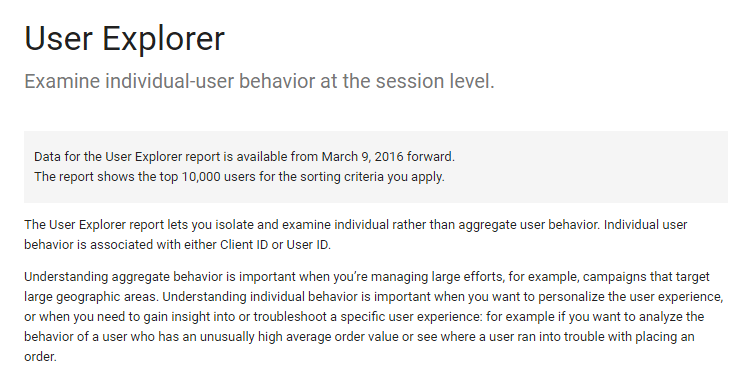
This section allows you to drill down into individual users' sessions, rather than just the aggregate of all users. You can see a lot of interesting information: how many times they visited the site, the dates and times of their visits, how long they were on the site each time, what pages they viewed, and more. It's pretty cool to see how real people navigate your site, from how they arrived ('acquisition' in GA-speak) to how long they spent on each page.
Here is a look at main User Explorer page (left) and one user's activity (right):
 |
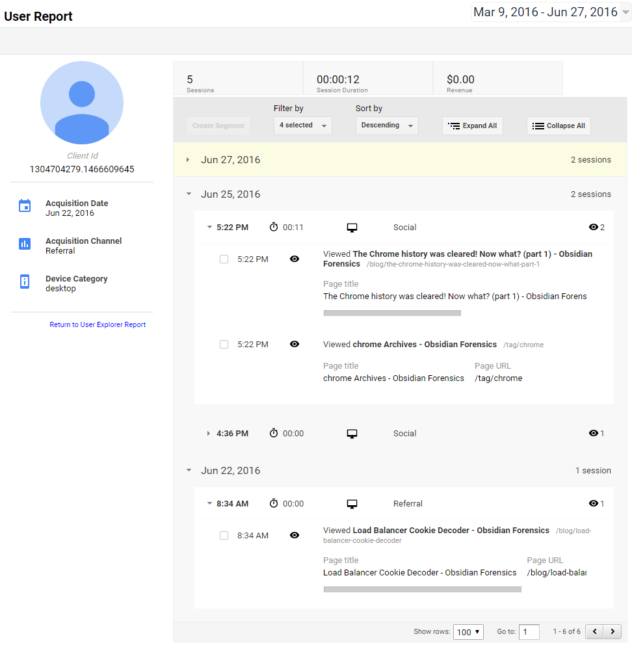 |
See anything familiar? The client IDs have the same format as the client IDs in the UA cookie. I was pretty amazed to see this, and my first question was whether these IDs were actually the same ones set on the client side in the _ga cookie.
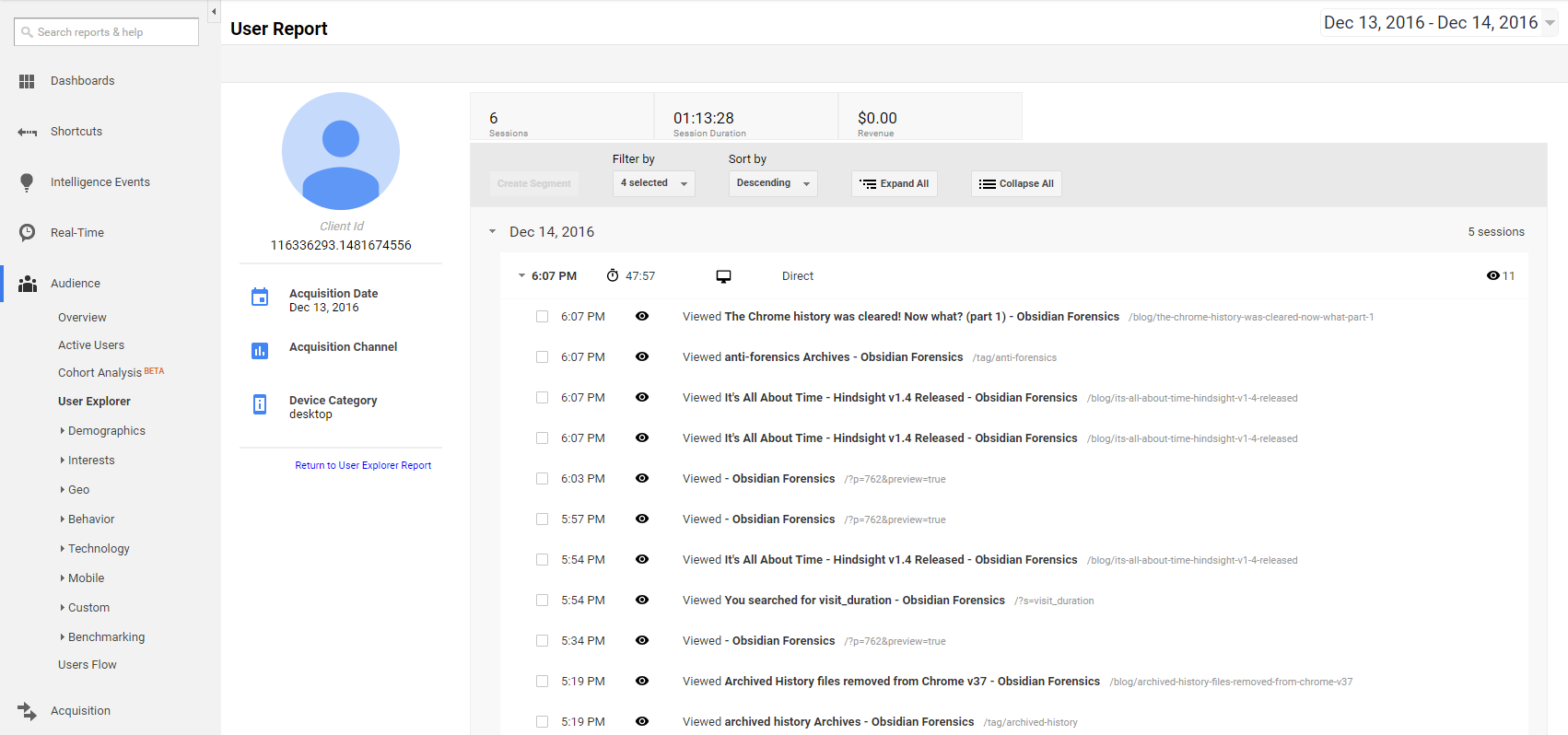
Turns out they are. I browsed around on obsidianforensics.com, then parsed by local Chrome history in Hindsight:
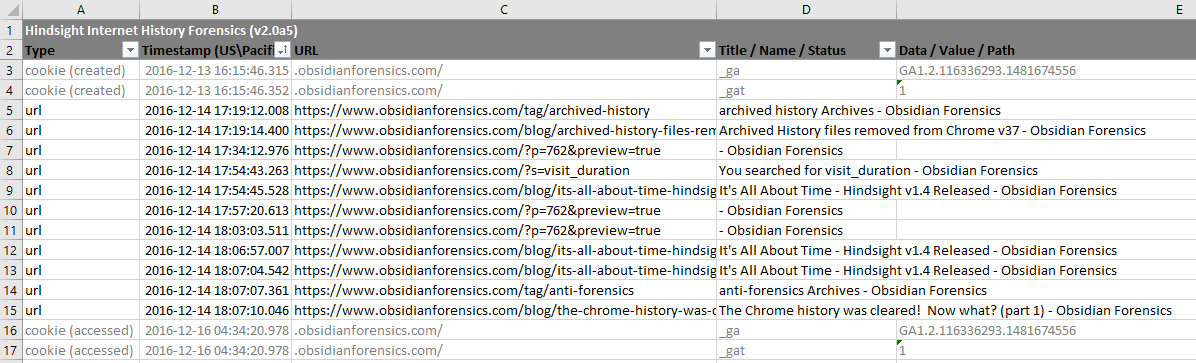
I then opened up the User Explorer, and searched for my client ID. Sure enough, there it was:
Adding Value to an Investigation
I thought this was pretty cool and could be a valuable addition to an investigation. To be sure, the User Explorer console won't be helpful in all situations, because the investigator needs to be able to access the report for the website in question. However, I could see it being very useful in some cases, particularly in corporate investigations. For example, in an internal investigation into an employee, being able to track what actions he or she took on the company's own website could be useful.
Even if you have access to a user's browser history, browsers only keep records for a limited time. If you have access to web proxy data, it often rolls over quickly due to space limitations. I could browse User Explorer data all the way back to March 2016, which is much farther than the three months of history Chrome retains. I don't know the reason for the March date; it just may have been when this feature was enabled for me, rather than a eight month limit.
I could see Universal Analytics and the User Explorer reports being helpful to me in a future investigation, and I hope it will help you out too. If you do find a use for this, drop me an email or leave a comment. It will be sad to lose Google Analytics cookies, but hopefully this has shown you how to get some value out of their successor.